- Install Local Docker Registry Ubuntu
- Install Local Docker Registry Tool
- Install Local Docker Registry Settings
- Install Local Docker Registry Windows
Estimated reading time: 4 minutes
Finally, install Docker: sudo apt install docker-ce Docker should now be installed, the daemon started, and the process enabled to start on boot. Check that it’s running: sudo systemctl status docker The output should be similar to the following, showing that the service is active and running. Docker Registry. This page contains information about hosting your own registry using the open source Docker Registry. For information about Docker Hub, which offers a hosted registry with additional features such as teams, organizations, web hooks, automated builds, etc, see Docker Hub. Docker commit -m 'added mariadb-server' -a 'Sunday Ogwu-Chinuwa' 59839a1b7de2 finid/centos-mariadb Note: When you commit an image, the new image is saved locally, that is, on your computer. Later in this tutorial, you’ll learn how to push an image to a Docker registry like Docker Hub so that it may be assessed and used by you and others.
This page contains information about hosting your own registry using theopen source Docker Registry. For information about Docker Hub, which offers ahosted registry with additional features such as teams, organizations, webhooks, automated builds, etc, see Docker Hub.
While it’s highly recommended to secure your registry using a TLS certificateissued by a known CA, you can choose to use self-signed certificates, or useyour registry over an unencrypted HTTP connection. Either of these choicesinvolves security trade-offs and additional configuration steps.
Deploy a plain HTTP registry
Warning:It’s not possible to use an insecure registry with basic authentication.
This procedure configures Docker to entirely disregard security for yourregistry. This is very insecure and is not recommended. It exposes yourregistry to trivial man-in-the-middle (MITM) attacks. Only use this solution forisolated testing or in a tightly controlled, air-gapped environment.
Edit the
daemon.jsonfile, whose default location is/etc/docker/daemon.jsonon Linux orC:ProgramDatadockerconfigdaemon.jsonon Windows Server. If you useDocker Desktop for Mac or Docker Desktop for Windows, click the Docker icon, choosePreferences (Mac) or Settings (Windows), and choose Docker Engine.If the
daemon.jsonfile does not exist, create it. Assuming there are noother settings in the file, it should have the following contents:Substitute the address of your insecure registry for the one in the example.
With insecure registries enabled, Docker goes through the following steps:
- First, try using HTTPS.
- If HTTPS is available but the certificate is invalid, ignore the errorabout the certificate.
- If HTTPS is not available, fall back to HTTP.
- First, try using HTTPS.
Restart Docker for the changes to take effect.
Repeat these steps on every Engine host that wants to access your registry.
Use self-signed certificates

Warning:Using this along with basic authentication requires to also trust the certificate into the OS cert store for some versions of docker (see below)
This is more secure than the insecure registry solution.
Generate your own certificate:
Be sure to use the name
myregistrydomain.comas a CN.Use the result to start your registry with TLS enabled.
Instruct every Docker daemon to trust that certificate. The way to do thisdepends on your OS.
Linux: Copy the
domain.crtfile to/etc/docker/certs.d/myregistrydomain.com:5000/ca.crton every Dockerhost. You do not need to restart Docker.Windows Server:
Open Windows Explorer, right-click the
domain.crtfile, and choose Install certificate. When prompted, select the followingoptions:Store location local machine Place all certificates in the following store selected Click Browser and select Trusted Root Certificate Authorities.
Click Finish. Restart Docker.
Docker Desktop for Mac: Follow the instructions inAdding custom CA certificates.Restart Docker.
Docker Desktop for Windows: Follow the instructions inAdding custom CA certificates.Restart Docker.
Troubleshoot insecure registry
This section lists some common failures and how to recover from them.

Failing...
Failing to configure the Engine daemon and trying to pull from a registry that is not usingTLS results in the following message:
Docker still complains about the certificate when using authentication?
When using authentication, some versions of Docker also require you to trust thecertificate at the OS level.
Ubuntu
Red Hat Enterprise Linux
Oracle Linux
Restart Docker for the changes to take effect.
Windows
Open Windows Explorer, right-click the certificate, and chooseInstall certificate.
Then, select the following options:
- Store location: local machine
- Check place all certificates in the following store
- Click Browser, and select Trusted Root Certificate Authorities
- Click Finish
Learn more about managing TLS certificates.
After adding the CA certificate to Windows, restart Docker Desktop for Windows.
registry, on-prem, images, tags, repository, distribution, insecureThis page contains information about hosting your own registry using theopen source Docker Registry. For information about Docker Hub, which offers ahosted registry with additional features such as teams, organizations, webhooks, automated builds, etc, see Docker Hub.
What it is
The Registry is a stateless, highly scalable server side application that storesand lets you distribute Docker images. The Registry is open-source, under thepermissive Apache license.
Why use it
You should use the Registry if you want to:
- tightly control where your images are being stored
- fully own your images distribution pipeline
- integrate image storage and distribution tightly into your in-house development workflow
Alternatives
Users looking for a zero maintenance, ready-to-go solution are encouraged tohead-over to the Docker Hub, which provides afree-to-use, hosted Registry, plus additional features (organization accounts,automated builds, and more).
Requirements
The Registry is compatible with Docker engine version 1.6.0 or higher.
Basic commands
Start your registry
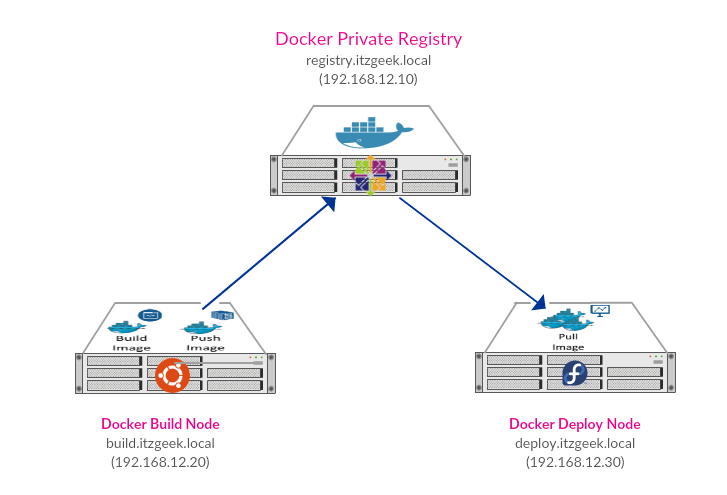
Pull (or build) some image from the hub
Tag the image so that it points to your registry
Install Local Docker Registry Ubuntu
Push it
Install Local Docker Registry Tool
Pull it back
Now stop your registry and remove all data
Next
Install Local Docker Registry Settings
You should now read the detailed introduction about the registry,or jump directly to deployment instructions.
Install Local Docker Registry Windows
registry, on-prem, images, tags, repository, distribution